Digital interconnectivity:How secure is sensitive company data?
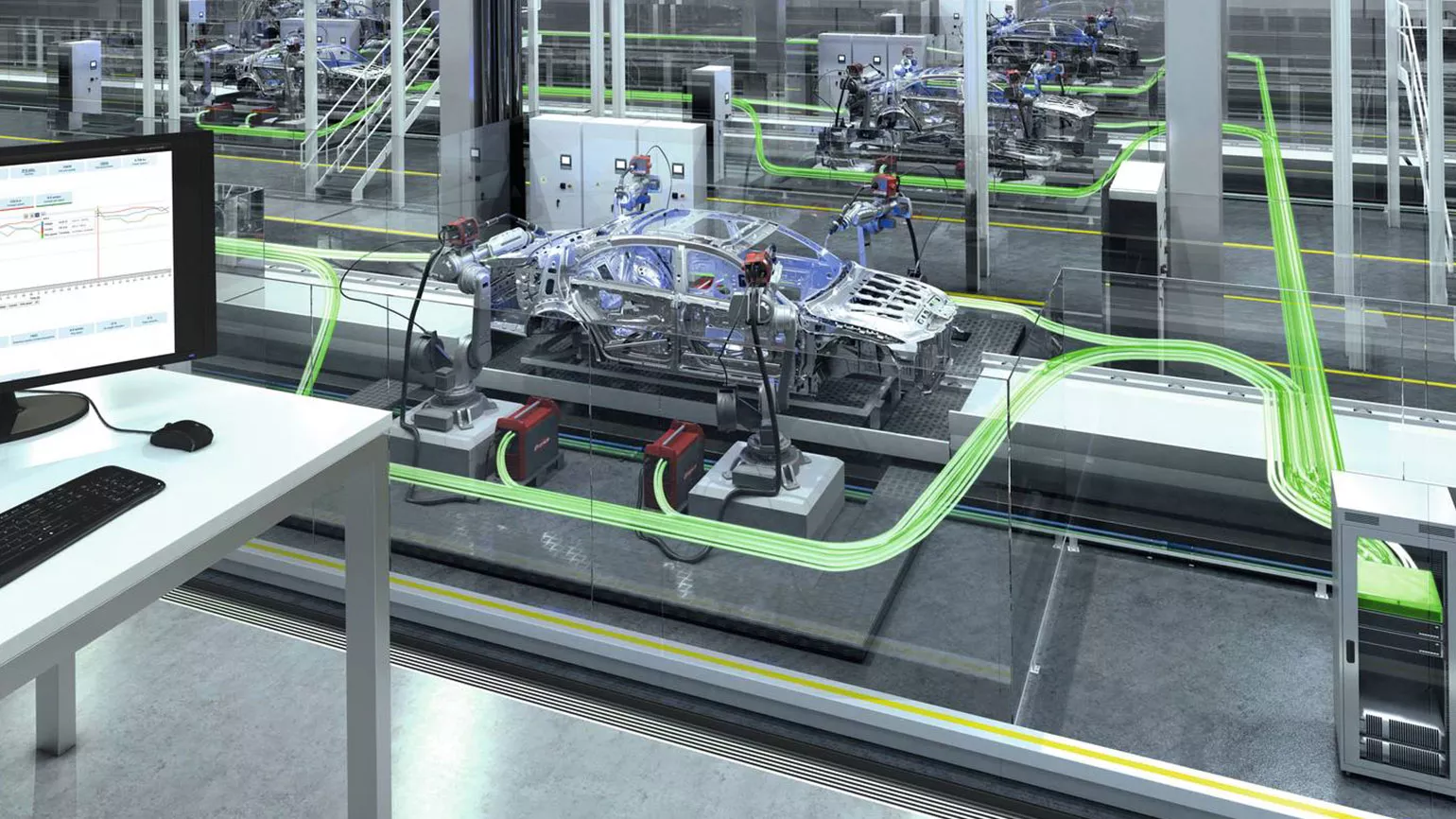
Advancing digitisation and the use of new, web-based communication technologies have long been evident in our private lives, for example in the way we listen to music or store and share photos. A similar development is also occurring in industrial manufacturing: machines, load carriers, components and goods are being linked together to form overarching valueadded chains, whose elements communicate and seamlessly interact with each other. For all this to be possible however, all the relevant product and process data must exist in digital form and be made available to all the stations involved.
MANUFACTURING MORE QUICKLY, FLEXIBLY AND CHEAPLY
Data processing and analysis is on the march in the world of welding technology. Modern welding systems collect information about the current, voltage, wire speed, welding speed and time, as well as arc and dynamic correction or job numbers. “With the aid of this data, welding processes can be optimised and errors can be avoided,” explains Roland Schick, Technical Product Manager Welding Datamanagement & Applications at Fronius Perfect Welding. “Users are also able to seamlessly integrate welding systems into a networked and automated production environment.” For this reason, Fronius developed its own data management system, WeldCube, that allows power sources to be connected to each other via a network and the data to be retrieved on various devices via a web browser.
Using this data, however, also comes with additional expense: collection, storage and evaluation requires not only the appropriate technology, but also time, resources and expertise – even more so for large quantities of data sets. “Mass data collection, for example of the nature undertaken by large search engine operators, is therefore of less interest to industrial manufacturing firms,” adds Schick. “Instead of big data, the trend here is towards smart data; in other words, saving only what is relevant, instead of everything.” Exactly what that is varies from application to application. Collecting data on external factors such as humidity and temperature can provide important insights for the welding process. Combining these with device and process data and analysing them together could form the basis for further optimisations.
PROTECTED AGAINST UNAUTHORISED ACCESS
An important aspect is the security of the information that has been collected and stored. In many cases this is sensitive company data, which must not be permitted to fall into the wrong hands under any circumstances. “We are aware of the risks of data misuse, both for data stored locally and that processed in the cloud. That is why we not only have internal IT-security experts, but also work closely with external specialists in data security,” Schick explains.
There are various ways of protecting data. One of these is to adopt the latest cryptography methods to encrypt and authenticate data. Data would ideally be transferred according to the ‘end-to-end’ principle: the sender encrypts the information in a trusted environment with a system that can only be decrypted by the receiver in a similarly secure environment. Certificates that verify the authenticity of the data and the sender are also used. “Our customers’ data is sacred, which is why we adhere to the best possible standards,” emphasizes Schick. “In spite of this, in most companies there is a great deal of scepticism around networking and data exchange. We are trying to dispel such prejudices and illustrate the advantages. Users have to experience the benefits that digitisation will bring to their workplace; then acceptance will come.”
Security also involves protecting machines and equipment, e.g. power sources, against attacks from hackers. Due to the high degree of networking in the Internet of Things, it is possible for unauthorised access to parts of the industrial manufacturing environment to occur – whether that is to steal valuable data and know-how or to sabotage production operations. This also presents a challenge for device manufacturers. “At Fronius, the security of software products is already taken into account during the design phase,” explains Roland Schick. However, the user must also ensure sufficient security measures are implemented in their networks. This starts with changing default passwords to secure passwords according the latest technological standards.
NETWORKING USED BY MANUFACTURERS AND CUSTOMERS ALIKE
For the future, the Fronius expert attests to the further potential of data collection in industrial applications: “With the right information, we can not only help our customers to optimise their welding processes, but also to take their requirements into account in our product developments.” The suggestions and wishes that Fronius service and application engineers bring back from their experiences in the field could thus be supported and made tangible through specific facts. “This data is also interesting to us. For example, we could see which software functions are being used most often, what we have to continue to develop and what we can simplify for the customer.” Schick is convinced that the software and data business will gain increasing significance for Fronius: “Whether it is for product and process updates or service and support; digital networking will allow us to help users more quickly, flexibly and cost-effectively in many matters. Trust in the new technology is a prerequisite for that.”